Stop Chasing Signatures
We have all seen the Signature Illusion: 100% policy attestation, green HR dashboards, and still no proof that the policy is alive in day-to-day work. A signature is a legal receipt, not operational evidence.
If you ask an engineer how a specific data classification rule applies to the log file they are troubleshooting, you usually get a blank stare.
The Signature Illusion
Policy attestation is a receipt. Behavioral verification is evidence.
The 5-Minute Workflow
- Ingest: Upload your policy PDF (AI Ethics, Data Handling, Access Control).
- Map: Svelto identifies behavioral controls and maps them to frameworks like SOC 2, ISO 27001, or NIST 800-53.
- Approve: You review the generated scenarios and approve them in seconds.
- Verify: Employees resolve moments of truth in 30 seconds, directly in their workflow.
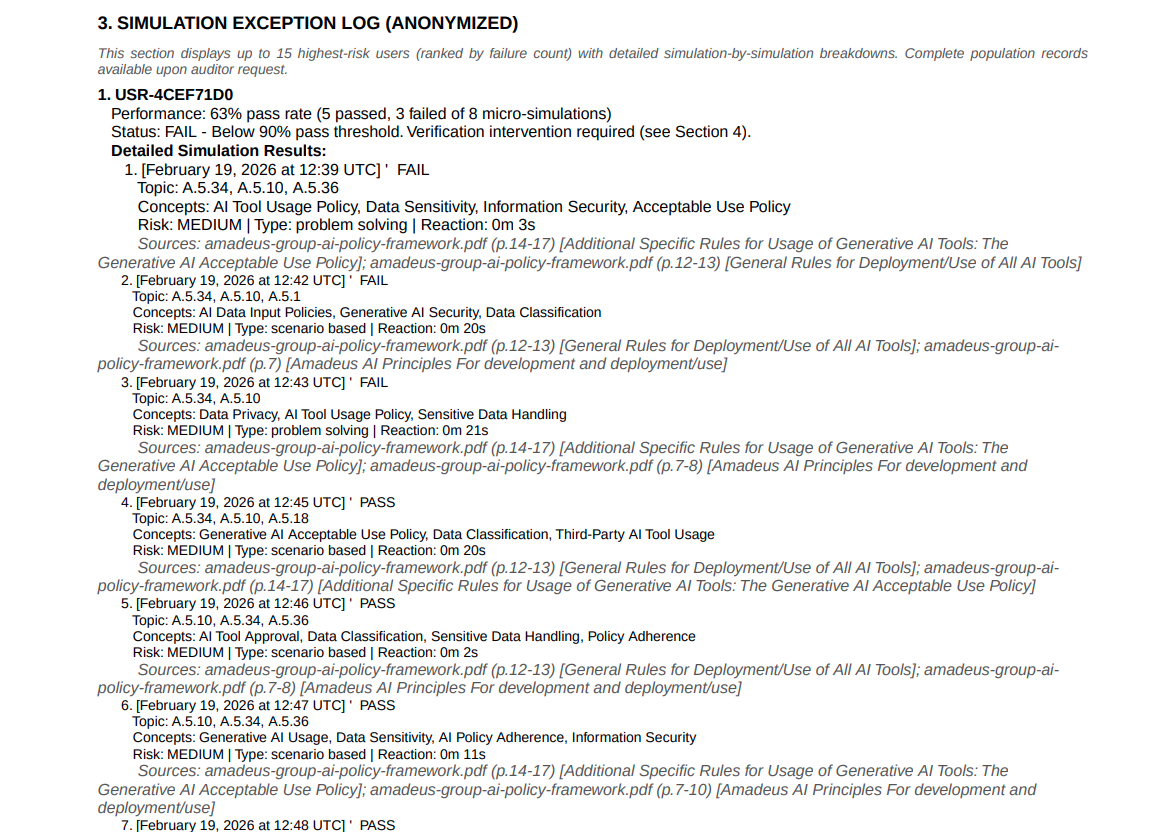
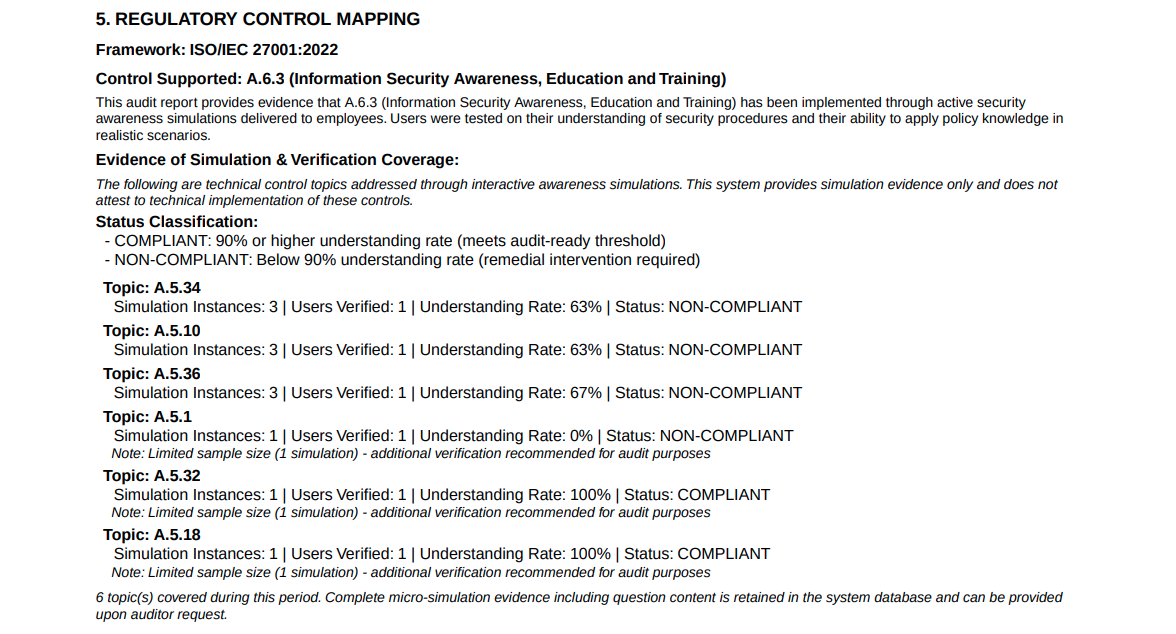
Evidence in Minutes
The audit report shows the real-world outcomes: who verified the right behavior, how fast they responded, and the exact controls covered. This is the difference between a training artifact and audit-ready proof.
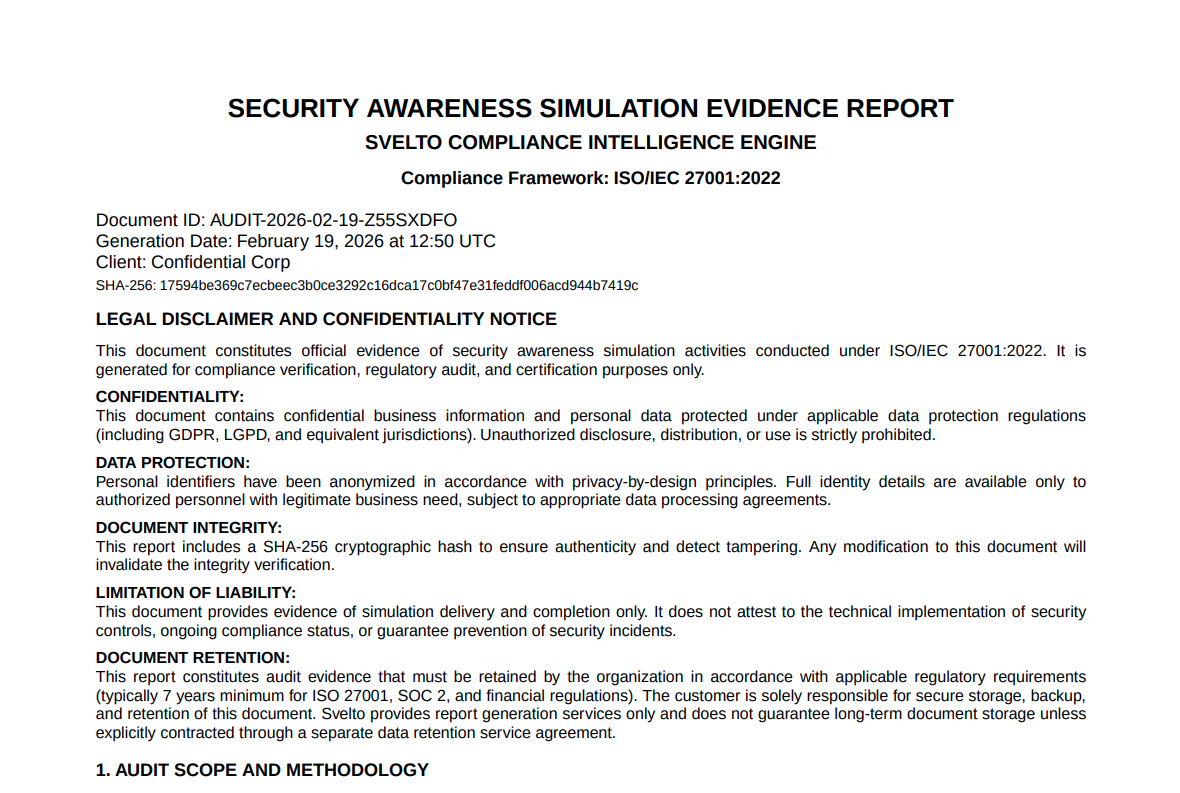
The Svelto Audit Packet
- Cryptographic Integrity: Every report includes a SHA-256 hash to detect tampering.
- Traceability: Each interaction maps to a specific control (e.g., A.5.34, A.5.10).
- Behavioral Telemetry: Evidence of reflex integrity and verification velocity.
Human Static Analysis
This is not training. It is human static analysis: verified behavior, produced while your team actually works. When the auditor arrives, you hand them a packet that proves operational reality.